If you’re a small business owner looking into data security options, it’s likely you’re hearing or reading quite a bit about ISO 27001. Data security standards can be quite confusing. Here’s a handy guide to help you better understand just what the ISO standards are (and why they matter to your business).
What is ISO 27001?
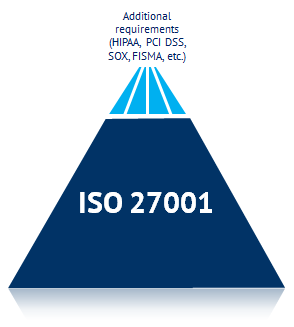
ISO IEC 27001 is an information security management standard. It provides guidance for businesses and organizations to ensure a high level of data security and is used to manage data security risks and controls within those businesses and organizations. Because of its broad approach, many businesses choose ISO 27001 as a guiding standard, and then customize their data security standards and processes to meet their specific compliance needs.
Follow this link to an excellent plain-English guide to ISO 27001. I’ve summed up the main points below.
What are the 11 main information security requirements governed by ISO?
1. A clear and current security policy
As in, regularly updated and reviewed, with specific processes and policies spelled out to be easily understood by any employee.
2. Organization of information security
Everyone in the business or organization must have a full understanding of the security policy, and his or her role in it.
3. Asset management
The inventory of information assets (hardware and software) should be continually updated to remain current. Changes to this inventory should be traceable back to a specific individual.
4. Human resources security
What data security controls are in place when an employee joins or leaves the organization? For example, if an employee is terminated, his or her system access should also be immediately terminated, so that they won’t be able to tamper with system data.
5. Physical and environmental security
The physical security of information assets (like a data center) must be protected through advanced authentication methods, so that a compromised system password wouldn’t jeopardize the security of an entire system.
6. Communications and operations management
Changes to the IT system must be planned, controlled, and documented. So that, for example, a last-minute engineering release doesn’t create a data security emergency in another department because of a lack of communication.
7. Access control
Access to sensitive data should be provided only to those who need it to perform their job duties. Detailed access logs should be kept and stored to ensure traceability and accountability.
8. Information systems acquisition, development, and maintenance
New systems and devices (hardware, software, etc.) should be fully examined and tested before going live in a work environment, to ensure they meet security standards.
9. Information security incident management
A comprehensive plan must be in place in the event of suspected suspicious activity or a possible security breach. For example, if there are numerous failed login attempts, how does the system respond? Who is alerted, and when?
10. Business continuity management
In the event of a disaster, your business or organization should be able to continue operations with restored data from backups. Your data backups should also be stored off-site (or in the cloud), so that they would be protected in the event of a natural disaster at your workplace.
11. Compliance
To be compliant with ISO 27001, you’ve got to show your compliance with the above processes through thorough documentation. This documentation will also prove handy when proving your compliance with other more specific, compliance authorities—like HIPAA, PCI, and SOX.
Why should ISO matter to you?
If you’ve read this much about ISO 27001, you’re clearly looking for a way to protect your company’s valuable data (after all, not many people read about data security for fun). And ISO 27001 is the perfect place to start.
If your systems and workstations meet ISO 27001 requirements, you’ll have the peace of mind that comes from knowing that you’re using some of the “best practices” in the data security industry to keep your business and clients safe. And by choosing a data security cloud or software solution that ensures ISO 27001 standards are in full force, you’ll be well on your way to meeting (or exceeding) the compliance guidelines specific to your industry, like HIPAA or PCI DSS.
 Today’s advanced data security providers allow business owners to set up fully ISO 27001-compliant systems, so that the basics are well-covered, then “tweak” and adjust as needed to meet specific compliance guidelines (for example, set up automated daily reports on data backups to ensure HIPAA compliance).
Today’s advanced data security providers allow business owners to set up fully ISO 27001-compliant systems, so that the basics are well-covered, then “tweak” and adjust as needed to meet specific compliance guidelines (for example, set up automated daily reports on data backups to ensure HIPAA compliance).
If you’d like to learn more about ISO 27001 compliance and other best practices when it comes to information security and your IT system, we cover these in great detail in our Services Guide. Download it to learn more about how you can outsource your IT needs to more easily comply with industry standards.
